Verification of Social Media Content
Overview and Purpose
Our discipline of verification as journalists continues to be challenged by misinformation, disinformation, and cyber-supported influence operations. The current post-truth information ecosystem threatens to further erode trust in journalism and our democratic institutions.
Outcomes
Students will learn to:
- Be skeptical and seek corroborating evidence to verify user-generated content shared on social media.
- Use open-source-intelligence techniques (OSINT) to find clues and corroborating evidence to verify images, videos, and information.
- Avoid amplifying fabricated news and propaganda.
Readings for Class
- User-Generated Content Guide From Online News Association and Ethics & Excellence in Journalism Foundation
- ABC Apologizes for Showing Video From U.S. Gun Range in Report on Syria New York Times, October 14, 2019
- Source hacking: How trolls manipulate the media CJR, September 12, 2019
- Verifying online information: The absolute essentials, First Draft. First Draft is a global non-profit at the Craig Newmark Graduate School of Journalism at CUNY that supports journalists, academics, and technologists working to address challenges relating to trust and truth in the digital age.
- First Draft’s Essential Guide to Responsible Reporting in an Age of Information Disorder
Class Discussion
How could ABC have avoided the mistake they made in the article you read, and how did the President react? How do you think a mistake like this one affects the public’s trust in journalism as an institution?
Discuss Chapter Four, Five and Seven, starting on page 25 of First Draft’s Essential Guide to Responsible Reporting in an Age of Information Disorder from the assigned readings. What are the dangers of covering manipulated or altered content? When is it appropriate to cover it and how can you do so responsibly?
Review in class First Draft’s Five Pillars of Visual Verification, from the above reading on essentials:
Discussion in class: Have students close their laptops and display the post below in class. NOTE that the original post has potentially disturbing content (based on the rest of the image’s inauthenticity, however, it’s likely the disturbing portion is not authentic either), so show this redacted version of the image below.
Have the class brainstorm what techniques and tools they could use to answer these questions about this social media post below, on an Indian Jet, and write them all out on a whiteboard:
- Provenance: Are you looking at the original account, article or piece of content?
- Source: Who created the account or article, or captured the original piece of content?
- Date: When was it created?
- Location: Where was the account established, the website created or piece of content captured?
- Motivation: Why was the account established, the website created or the piece of content captured?

Compare the techniques students brainstormed as a group with this First Draft One-Sheet of Photo Verification Steps
Walk through the following steps for the class:
If you do some research on the poster of the above Tweet, he is Wajahat Kazmi, has a verified account on Twitter, and is a local journalist in Pakistan.

He didn’t just join Twitter yesterday, which would be a red flag, If you look at his Twitter posts (“Media posts,” posts of photos and videos, can be useful to focus on), he posts about legitimate issues, things and places a Pakistani journalist would post about. You can also find him on LinkedIn https://www.linkedin.com/in/kazmiwajahat/?originalSubdomain=pk
The next step is to try to verify the photos from his post. Ask students to define a “reverse image search.” You can Install RevEye reverse image search extension — RevEye allows you to right-click on an image, to run a reverse image search through five different search engines including Google, Yandex, and TinEye. You should try multiple reverse image searches, because each one has potentially different results, and may have what you need.

When the Google Reverse Image search results come up, click on the Tools button

Which will bring up date ranges to choose, if you choose the custom option, you can set the date range to one before the date of the post in question:

Then the results will show you whether that image may have been posted on an earlier date.
In this case, the reverse image search results show that this photo is actually from a June 2016 crash:

Hence, the photo in the post we are verifying is not authentic, calling into question the entire post (which you can keep investigating for provenance, source, etc.) So you should not share this social media post or use it as evidence to corroborate your reporting. This reverse image search technique can potentially let you know quickly, whether a social media post includes an inauthentic or misidentifying photo as evidence for what the social media post is claiming or asserting is true.
Agence France Press used a reverse image search to debunk these photos:
- Is this the photo of an Indian Air Force jet shot down by Pakistan?
- No, these two photos do not show Indian Air Force jets shot down by Pakistan
Why does this matter? Amplifying disinformation by, in this case, sharing these easily debunkable photos, means that you would be spreading propaganda about the “informational conflict … of February’s India-Pakistan crisis, which threatened to escalate to all-out war. “ [Washington Post, 4/17/19]
Although many reliable news outlets shared this disinformation in February 2019, the photos and videos shared in social media posts were debunked, and ultimately, a Foreign Policy report from April 2019, says it that based on an official US military assessment, this incident did not happen. Did India Shoot Down a Pakistani Jet? U.S. Count Says No.
If you are interested, Bellingcat does a deeper dive into verifying claims that pictures released by Pakistan that purportedly showed parts of an F-16, purportedly downed by India.
Bellingcat is an independent international collective of researchers, investigators and citizen journalists using open source and social media investigation to probe a variety of subjects – from Mexican drug lords and crimes against humanity to tracking the use of chemical weapons and conflicts worldwide.
Verifying Video Shared on Social Media
To give students an understanding of what reporters are up against, watch this video in class: How to spot manipulated video | The Fact Checker at Washington Post
Review this First Draft One-Sheet of Video Verification Steps
Here is a tool to help analyze videos:
As a class read about the InVID Verification Tool here, and then install the Chrome plugin, InVID Verification Plugin. This tool will isolate thumbnails from videos, which will then allow you to do a reverse image search using the thumbnails via TinEye, Yandex or Google reverse image search.
Do this demonstration in class:
After installing the InVID Plugin, go to this tweeted video in class: https://twitter.com/steve_hanke/status/10882063806197078016

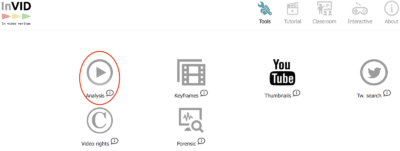
Choose the InVID toolkit plugin from your toolbar in Chrome and choose Open InVID:

Choose the “Analysis” button
Then paste in the url of the Twitter Video in question, and click the submit button:

InVID will isolate a thumbnail or multiple thumbnails which you can check in reverse images searches through the InVID platform.

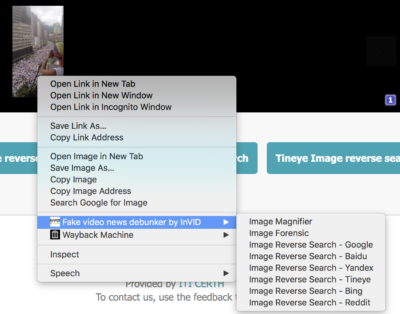
Right-click on a thumbnail in InVID and go to the Fake video news debunker by InVID. Choose the Google reverse search, in this case, but understand that each of those reverse images searches might have useful leads to aid your verification. Yandex, a Russian platform, has an especially good reverse image search.
The results of the Google reverse image search show that this image has circulated as far back as September 2016. So you should not share this social media post or use it as evidence to corroborate your reporting.


Review in class with students the array of verification and OSINT tools available on Bellingcat’s Online Investigative Toolkit
In-class Exercise
In-class Exercises
You have two options:
1) Pick some exercises from the Verif!cation Quiz Bot on Twitter
2) [The following examples courtesy of First Draft] Split your class into four groups and take 20 minutes to work on these examples:
- Group 1 Example: Can you locate this video and ascertain whether it matches the date on the tweet? https://twitter.com/bocavista2016/status/1009813474556252161
- Group 2 Example: Can you locate when this video is taken? https://twitter.com/jairbolsonaro/status/1010178315590733825
- Group 3 Example: Can you work out whether this site can be trusted? https://orientaltimes.co/ (tip – look to see if you can find the old version of the website – otimes.tv using a domain search tool like Whoxy.com)
- Group 4 Example: Can you work out who the person is that took this picture, and find a telephone number if you were asked by an editor to contact him. ALSO – find the latitude and longitude! https://www.instagram.com/p/BCf0A_ovMf3/
Discuss the methods used to verify information about these posts and what your students discovered about their authenticity.
Additional Resources
How you can help transform the Internet into a place of trust. An April 2019 TED Talk by Claire Wardle of First Draft
Verification: The Basics with Instructors: Craig Silverman, Claire Wardle, from DataJournlism.com
The Verification Handbook Authored by leading journalists from the BBC, Storyful, ABC, Digital First Media, and other verification experts.
A Guide to Open Source Intelligence (OSINT) Columbia Journalism Review
3-2-1 Exit Ticket Assessment
Have students answer these three brief concluding reflection questions on paper or through an online service like Socrative:
3. Write down three takeaways from this lesson;
2. Write down two questions you still have after this lesson;
1. Write down the one thing you enjoyed the most about this lesson.
